单选题In PIX versions prior to 7.x, multi-channel protocols were fixedup using the ’fixupprotocol’ command. Inversion 7.0 and higher the ’fixup protocol’commands were replaced by what commands?()Aaudit Bsecure Cinspect D The fixup protocol commands did not c
题目
audit
secure
inspect
The fixup protocol commands did not change in
相似问题和答案
第1题:
A.f->prior=p;f->next=p->next;p->next=f;p->next->prior=f;
B.p->next=f;f->prior=p;p->next->prior=f;f->next=p->next;
C.f->prior=p;f->next=p->next;p->next->prior=f;p->next=f;
D.p->next=f;p->next->prior=f;f->prior=p;f->next=p->next;
第2题:
A.XID
B.VERSIONS_PK
C.VERSIONS_XID
D.VERSIONS_UNIQUE
第3题:
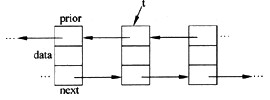
某双向链表中的结点如下图所示,删除t所指结点的操作为(54)。
A.t->prior->next=t->next;t->next->prior=t->prior;
B.t->prior->prior=t->prior;t->next->next=t->next;
C.t->prior->next=t->prior;t->next->prior=t->next;
D.t->prior->prior=t->next;t->next->prior=t->prior;
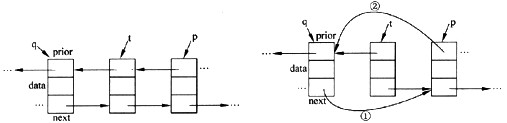
解析:本题考查链表的基本运算。设q指向t的前驱结点,P指向t的后继结点,如下所示。
可知,q=t->prior,p=t->next。
删除t所指结点的操作为:
①q->next=p;
②p->prior=q。
由于题目中没有给出指针p和q,所以将①、②中的p和q分别代换为“t->next”和“t->prior”,则得到
t->prior->next=t->next
t->next->prior=t->prior
第4题:
在图4-13拓扑结构中PIX 525防火墙有如下配置语句,请写出每条配置语句的功能注释。
Pix525(config) route outside 0 0 211.156.169.1 (1)
Pix525(config) static(inside,outside) 211.156.169.2 211.156.169.5 (2)
Pix525(config) conduit deny icmp any any (3)
Pix525(config) fixup protocol http 8080 (4)
(1) 定义一条指向边界路由器(或下一跳IP地址为211.156.169.1的路由器)的默认路由。 (2) 建立内部IPDMZ区地址172.30.98.56 211.156.169.5 与外部IP地址 172.32.65.98 211.156.169.2之间的静态映射。 (3) 禁止icmp消息任意方向通过防火墙。 (4) 启用HTTP协议,并指定HTTP的端口号为8080 解析:(1)在配置模式下命令“route”用于设置指向内网和外网的静态路由。其语法格式如下:
routeif_name>0 0 gateway_ip[metric]
其中,“if_name”是接口名字,例如inside、outside;“gateway_ip”是网关路由器的IP地址;“metric”是到gateway_ip的跳数,其默认值为1。
配置语句route outside 0 0 211.156.169.1表示一条指向边界路由器(或下一跳IP地址为211.156.169.1的路由器)的默认路由。
(2)在配置模式下,命令“static”用于配置静态NAT功能。如果从外网发起一个会话,会话的目的地址是一个内网的IP地址,“static”命令就把内部地址翻译成一个指定的全局地址,允许这个会话建立。其命令格式如下:
static(internal_if_name.external_if_name)outside_ip_address inside_ip_address
其中,“internal if name”是内部网络接口名字,如inside等;“extemal_if_name”是外部网络接口名字,如outside等;“outside中address”是外部IP地址;“inside_ip_address”是内部IP地址。
配置语句static(inside,outside)211.156.169.2211.156.169.5用于建立DMZ区地址211.156.169.5与外部 IP地址211.156.169.2之间的静态映射。
(3)管道命令(conduit)用于允许数据流从具有较低安全级别的接口流向具有较高安全级别的接口,例如允许从Internet网到DMZ(或内部接口)方向的会话。“conduit”命令的配置语法如下:
conduit permit | deny global_ip port-port> protocolforeign_ip
其中,“permit”为允许访问策略,“deny”为拒绝访问策略;“global_ip”是指由“global”或“static”命令定义的全局IP地址,如果“global_ip”为0,可用any来代替0,如果“global_ip”为某台主机,则需使用host命令参数;“port”是指服务所作用的端口,可以通过服务名称或端口数字来指定端口;“protocol”是指连接协议,例如TCP、UDP、ICMP等;“foreign_ip”表示可访问“global_ip”的外部IP地址,对于任意主机,可以用any表示,如果“foreign_ip”是一台主机,则需使用host命令参数。
配置语句conduit deny icmp any any表示禁止icmp消息(如ping的回声请求/响应消息)的任意方向通过防火墙。
(4)“fixup”命令用于启用、禁止、改变一个服务或协议通过PIX防火墙。由“fixup”命令指定的端口是PIX防火墙要侦听的服务。配置语句fix up protocol http 8080表示,启用HTTP协议,并指定HTTP的端口号为8080。
第5题:
The journal entry to record the cost of warranty repairs that were incurred during the current period, but related to sales made in prior years, includes a debit to Warranty Expense.()
第6题:
A、struggle
B、playing
C、trying
D、to try
第7题:
YouaremaintainingyourOLTPdatabaseinOracle10g.YouareperformingtheFlashbackTransactionQuerytofindtheundoSQLstatementsthatcanbeusedtoundothechangesmadetothedatabaseinthespecifictimeperiod.WhichpseudocolumnwillyouusetoperformtheFlashbackTransactionQuery?()
A.VERSIONS_STARTSCN
B.VERSIONS_STARTTIME
C.VERSIONS_XID
D.VERSIONS_OPERATION
第8题:
A.p->next->prior=p->prior;p->prior->next=p->next;
B.p->next=p->next->next;p->next->prior=p;
C.p->prior->next=p;p->prior=p->prior->prior;
D.p->prior=p->next->next;p->next=p->prior->prior;
第9题:
A.p->prior->next=p->next;p->next->prior=p->prior;
B.p->prior=p->prior->prior;p->prior->prior=p;
C.p->next->prior=p;p->next=p->next->next;
D.p->next=p->prior->prior;p->prior=p->prior->prior;
第10题:
Communication protocols are(66)connection-oriented or connectionless,(67)whether the sender of a message needs to contact and maintain a dialog with the recipient or(68)send a message without any, prior connect and with the hope that the recipient receives everything.(69).These methods(70)the two ways that communication is implemented on networks.
A.not
B.neither
C.either
D.all
